For software developer and hardware vendors, sometimes it may difficult for them to make decision when they have to evaluate and select protection solution (Packer/Protector tools) from the market to protect their software product.
Why Select Protection tools is so important.
Using the software protection tools to secure your investment in development and marketing expense and protect your code, valuable IP, critical algorithm and data;
Monetized your software and pursue opportunity to different market segment;
There are many different kind of software protection solution available in the software utility market, with different protection technology adapted and using some highlight marketing language to package their product and it makes difficult for developer to decide which protection toolkit is best and most suitable to protect their working effort.
In general, The Software Protection solution (no matter what we call these software toolkit:Shell, Packer or Protector) is the protection toolkit incorporated multiple technology to protect developer's software products: code, IP, data, etc. With the protection toolkit, it help the software or hardware vendor to prevent their investment and working effort (Intellectual Property, Algorithm) from the cracking or piracy by hacker or illegal users.
There are many protection tool available in the software protection market which protection function and security level is different due to different security technology implemented.
Here are some recommendation and experience shared with you.
1. The Packer (some tools named with Software Wrapper or packer) with Compression functionality: the main protection function of these protect tools is hide the code and data of original program, and compress the program code hided. The challenge to this kind of tool is that of original code and data will be decompressed to original code or data when program executed. So the security level of this "compression" shell is quite limited.
2. The Protector with Encryption/decryption function; besides of compression function to software, these kind of wrap/protection tool achieve higher security level to protected software by using multiple encryption technology and combine API calling to sign/verify signature the license. Developer may encrypt the code, data, algorithm of software, also may encrypt to specified functions of program, and decrypt these encrypted data, code when program executed.
3. The Protector tools with VM based functionality; VM based tools leveraged different kind of protection technology: compression, encryption/decryption the software code and API calling. These kind of protection tools also introduce Virtual Machine technology to achieve maximum security level to the protected software with anti-debug and anti-reverse engineering technology available.
The original instruction will be virtualized and interpreted into self-defined VM instruction. since the instruction to VM is not open published and every time it will generates a random VM instruction when start to protect software, so, it is almost impossible for hacker to crack or tamper the protected software and get the original code/algorithm when they use reverse-engineering/debug tools to analysis the VM instruction, code and also to analysis the VM.
So, the most secured Protector in the market is VM based protector tool. It combined multiple encryption/decryption, sign and signature verification, and VM technology and provide highest level protection level to software program.
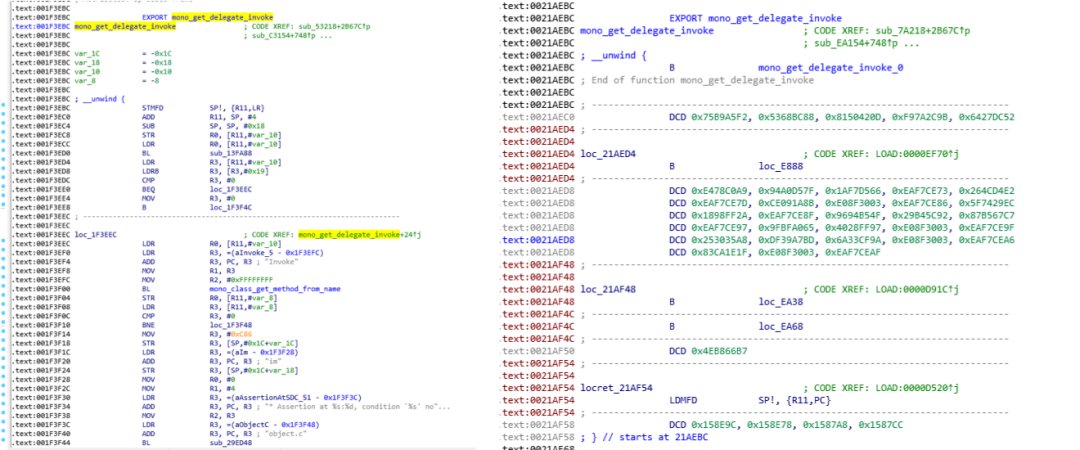
The source code before and after obfuscation protection technoloty of Virbox Protector:
6 evaluation criteria to evaluate the software protector
1. Security
The main purpose for developer to select and use the protection tools is protect the original code, algorithm, data with increasing the difficulty of cracking when hacker using the reverse engineering or debug tools, so the first priority to developer is evaluate the security of the protection tools. Select the most secured protection tool to protect your software, usually the security can be evaluate with 2 criteria:
1.1, Basic/fundamental protection function which means how does the tool may protect the software in general, by which technology and how to increase the crack difficulty and extend the crack time and cost.
For desktop program be protected, these basic protection feature would be contained following features: Compression, resource encryption, anti-debug, anti-reverse engineering, import table protection, etc.
For .Net program, Basic protection may include: compression, name obfuscation, anti-debug, etc.
1.2, whether or not to protect to specified functions of program
It is necessary to protect the specified program functions with obfuscation, virtualization to increase the security level and protect to your critical algorithm or IP.
2. Stability of protected software when executed
With different kind of protection technology implemented to protect your software, it will increase the complexity of your software, with some special protection features, sometime it will decrease the stability of software when executed, software may collapse in execution. Or the protected software will be treated to be virus contained and killed by anti-virus tools. If so, it will extremely decrease the user experience and bring negative influence to working efficiency.
Tips: try to select the more mature protector in the market.
3. Performance
The performance of protected software in execution will be affected due to multiple protection technology implemented. The more protection mode implemented to protect the software, the worse performance will be affected when software executed. So developer may consider and find a balance between the security and software execution performance when they design and develop their protection scheme to software. In the past, the software performance will be identified when whole protection development complete, now, some protection tool provide the performance analysis feature to developer, this feature is most effective and quite useful feature to developer during development and save lot of time and code effort in protection period. Developer may use this feature to analysis and adjust protection mode to specified "part" of software and finally make the best balance between the security and execution performance.
Tips: try to select the protection tool with performance analysis feature to protect your software, which will save lot of your time and get the best security level to your software.
4. The capability to support cross platform and compatible to multi language
The operation environment to software application will extend to multiple operation system and different language: from traditional desktop system to embedding, IoT platform, so when you evaluate the capability of protection tool to support cross platform and compatible to multi language, suggest you may evaluate it from following sector:
4.1. CPU Architecture supported: X86, X64, ARM32 and ARM 64 instruction set;
4.2. Operation System: Windows, Linux, macOS, Android, ARM Linux, etc.
4.3. Program language: the local executed program which compiled with static language: C/C++, Delphi, go; The .Net Program which compiled with C#, VB language; The Unity3D program which popular used in gaming program; Java based program; The program with python, PHP the script language;
5. Data protection:
For some program, some critical data may upload to implement a specific function or feature when software executed, and these critical data (e.g. machine learning data or other critical data) also need to be protected together with program code itself. So you need to check if the software protector may protect the data or image file. And how to prevent the leakage of data file when program executed.
6. User experience:
easy to use, with friendly GUI and provide command line interface for those developer who want to use API calling way to enhance the security to special code/algorithm. Also need to evaluate if the sample or demo available and service support and competence.
For more information to software protection solution, please contact with us info@seneselock.com, we'd like to help you and discuss related question with you.